By 2026, the CPA firm inbox will no longer be a convenience. It will be a liability.
For years, email attachments have been the default way to exchange tax returns, payroll data, financial statements, and client documents. But regulatory pressure, cyber insurance requirements, AI-driven phishing, and rising client expectations have changed the risk landscape.
Forward-thinking Accountants and CPAs are now replacing attachment-based workflows with secure portal ecosystems.
This is no longer optional. It is strategic.
Why Email Attachments Are Now a Compliance Risk
US accounting firms operate under growing regulatory scrutiny.
The FTC Safeguards Rule requires:
- Written Information Security Plan
- Risk assessments
- Encryption of client data
- Access control management
- Continuous monitoring
The IRS also expects tax professionals to maintain strict data protection protocols.
Email attachments introduce structural weaknesses:
- Attachments can be forwarded without control
- Limited audit trail visibility
- Inconsistent encryption practices
- High phishing exposure
- No structured version control
By contrast, firms using modern Accounting Firm Systems can centralize document exchange inside controlled environments.
This directly supports regulatory defensibility.
Cyber Insurance Is Raising the Bar
Cyber insurers are tightening underwriting standards for CPA firms.
Most policies now require:
- Multi factor authentication
- Encryption enforcement
- Documented access logs
- Formalized security controls
Attachment-heavy workflows weaken your position during breach investigations.
Structured environments such as Back Office Support Systems create defensible documentation and audit trails.
The inbox cannot serve as a primary document management system in 2026.
AI Phishing and the 2026 Threat Landscape
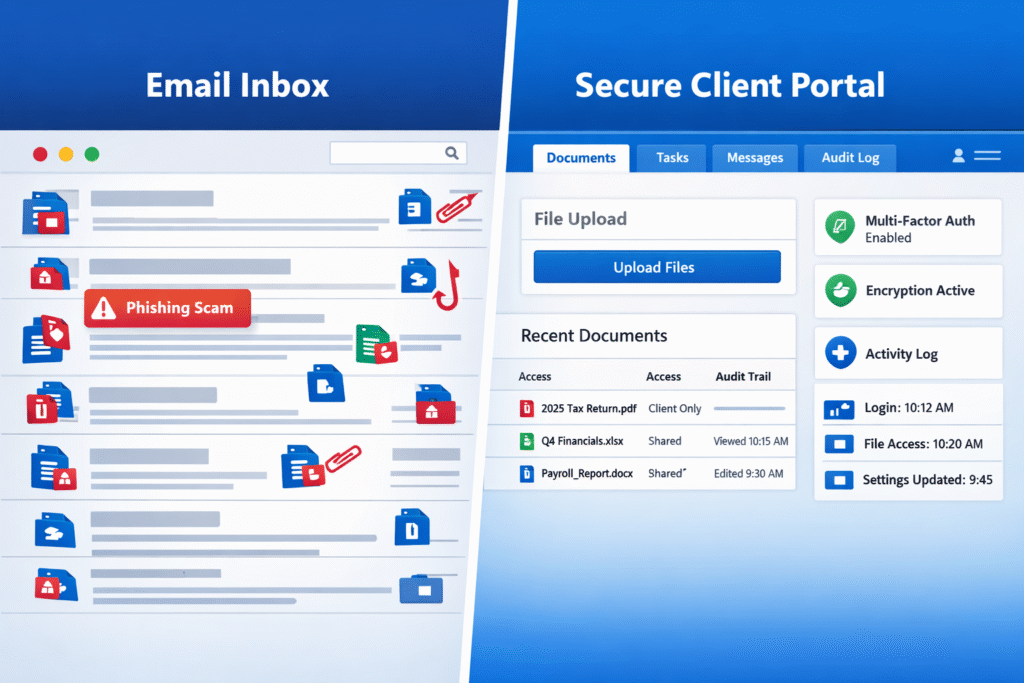
AI generated phishing attacks now mimic client communication patterns with precision.
Common attack vectors include:
- Fake K 1 uploads
- Fraudulent 1099 spreadsheets
- Spoofed payroll PDFs
- Malware embedded in tax documents
When attachments are routine, malicious files blend into workflow.
Secure portal-based collaboration creates a behavioral shift. Clients upload only inside authenticated systems. Unexpected attachments become immediate red flags.
This single change dramatically reduces attack surface.
Client Experience Has Entered the Security Era
Clients no longer evaluate firms only on tax accuracy.
They evaluate:
- Data protection
- Collaboration structure
- Technology stack
- Transparency
- Responsiveness
A structured system similar to what we outline in Remote Accounting Workflow Setup provides visibility and clarity.
Email threads do not.
Real examples of structured transformation can be seen in this CPA Firm Cloud Migration Case Study.
Security is now part of client experience.
Email Attachments vs Secure Portals
Factor | Email Attachments | Secure Client Portal |
Encryption | Inconsistent | Encrypted in transit and at rest |
Access Control | None after forwarding | Role based permissions |
Audit Trail | Limited | Complete activity logs |
Version Control | Poor | Structured document history |
Phishing Exposure | High | Significantly reduced |
Regulatory Defensibility | Weak | Strong |
The inbox was built for communication.
It was not built for regulated financial data exchange.
Operational Impact on Scaling Firms
Firms managing offshore or remote teams must maintain structured workflows.
Email attachments create:
- Duplicate versions
- Confusing review chains
- Lost documentation
- Inefficient handoffs
Secure environments align with scalable infrastructure discussed in Cloud vs On Prem Accounting for CPA Firms.
Structured audit-ready collaboration also supports modern Audit Support Frameworks.
Scaling without structure increases risk.
The AI Governance Shift in CPA Firms
The accountant’s role is evolving.
As described in our article on AI in Tax Preparation Tools, AI now assists with:
- Data extraction
- Review automation
- Error detection
- Reporting support
The CPA is becoming a governor of AI systems, prioritizing judgment, oversight, communication, and ethics over manual processing.
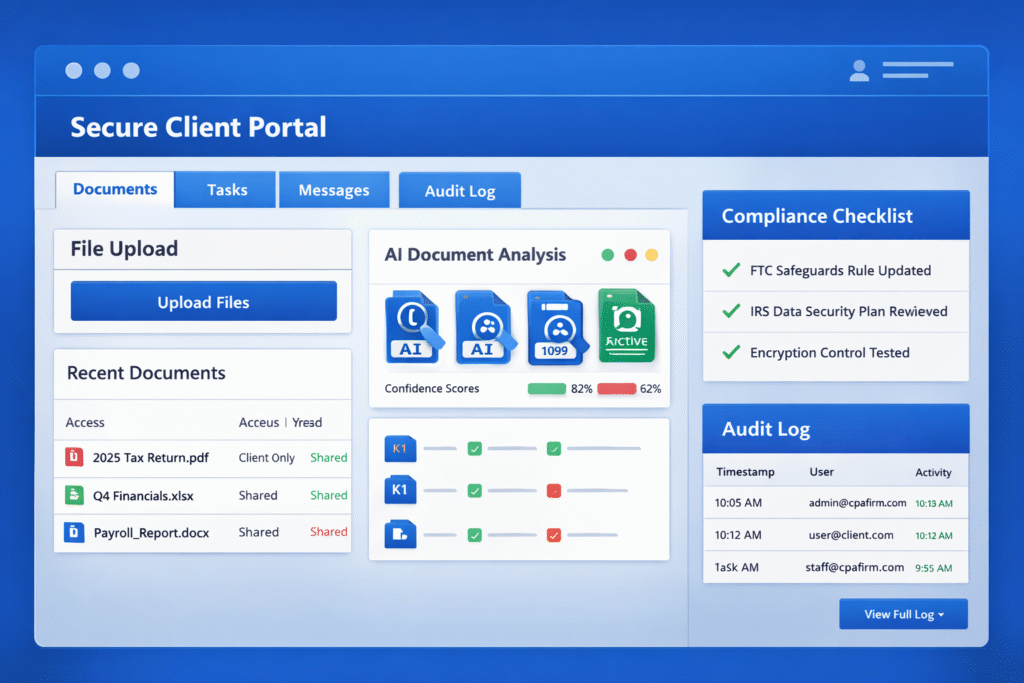
Continuous compliance will soon become operational reality. Secure systems can automatically:
- Flag deviations from the Written Information Security Plan
- Detect abnormal download activity
- Update security protocols in real time
Email attachments interrupt automation pipelines.
Secure portals enable structured AI integration.
Expert Insight
“Firms underestimate how often data breaches originate from predictable behavior patterns. Email attachments create predictability. Secure portals create control.
Bindesh Jain, Tax Director (CA, CS), SafeBooks
Security Culture as a Market Differentiator
Firms evaluating outsourcing, scaling, or structured collaboration increasingly review infrastructure maturity. This is central when selecting partners for complex compliance work such as SALT, international reporting, or multi entity filings.
See how structured teams operate in this overview of How to Evaluate an Offshore Accounting Partner.
A security first culture is no longer internal policy. It is a sales advantage.
Comparison Summary
Business Objective | Attachment Based Workflow | Portal Based Workflow |
Reduce breach risk | Reactive | Proactive |
Improve audit readiness | Limited traceability | Full traceability |
Support remote teams | Fragmented | Structured |
Strengthen client trust | Moderate | High |
Enable AI integration | Disrupted | Optimized |
The Strategic Decision for 2026
Eliminating attachment based workflows signals:
- Compliance readiness
- Insurance defensibility
- Scalable operations
- AI integration capability
- Client trust prioritization
The secure portal is the foundation of the modern advisory relationship.
The inbox is the weakest link.
If your firm is ready to modernize collaboration, strengthen compliance posture, and build secure infrastructure, visit our Contact Us page to start the conversation.
FAQS
Are email attachments prohibited for CPA firms?
Does the FTC Safeguards Rule require encryption?
Can cyber insurance deny claims due to weak email practices?
Do small CPA firms need secure portals?
How do secure portals improve client experience?

Director (CA, CS)
A Chartered Accountant and Company Secretary with over 11 years of experience, Bindesh specializes in direct taxation, estate planning, and statutory compliance. He helps U.S.-focused firms navigate complex tax issues with precision and foresight, while ensuring every SafeBooks engagement meets legal and procedural expectations.